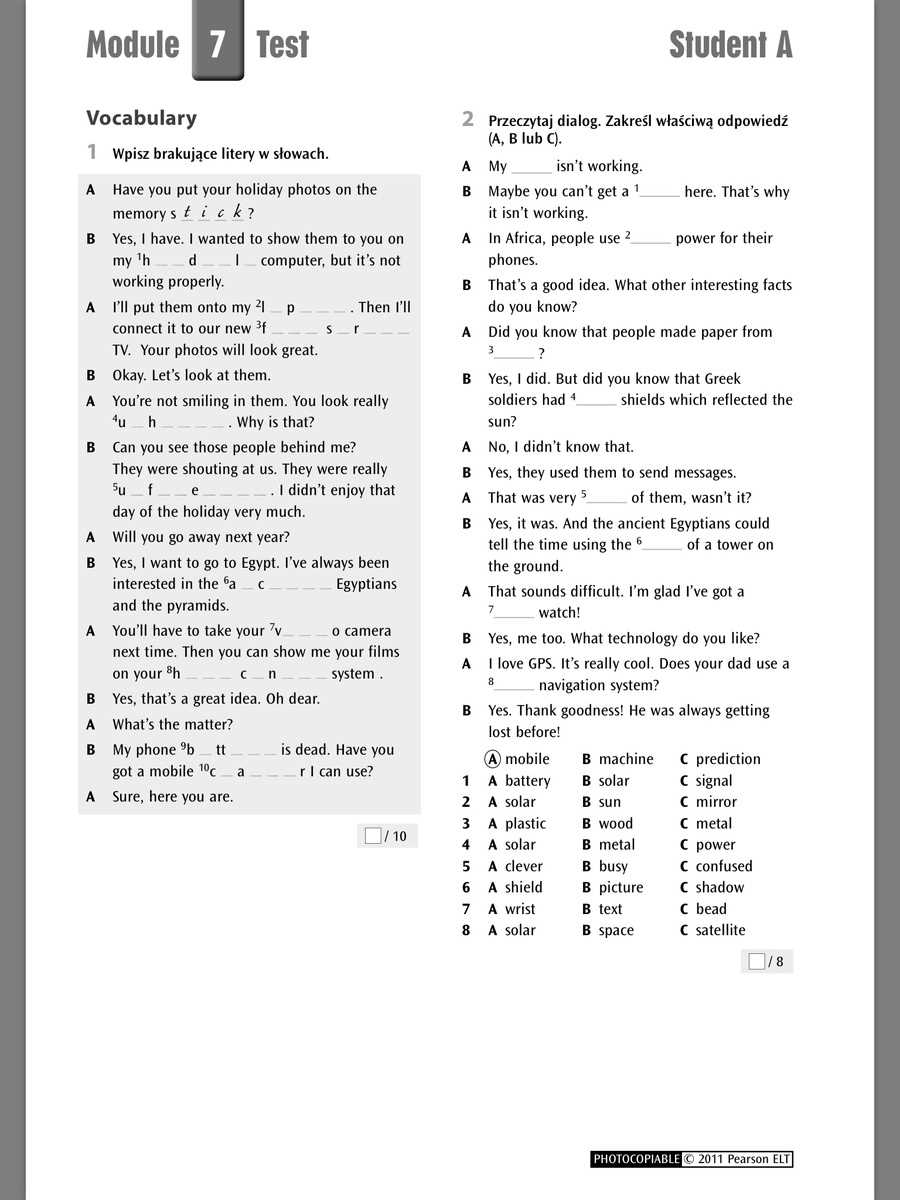
Unmasking the Enemy: The Crucial Role of Force Protection Module 4 Counterintelligence Pretest in Modern Warfare
Unmasking the Enemy: The Crucial Role of Force Protection Module 4 Counterintelligence Pretest in Modern Warfare
As the world becomes increasingly complex and interconnected, the threat of terrorism and insider threats has never been more pressing. To combat these risks, military forces and law enforcement agencies have turned to advanced counterintelligence tools, such as the Force Protection Module 4 (FPM-4) Counterintelligence Pretest. This cutting-edge technology has revolutionized the way we identify and mitigate insider threats, but what exactly is the FPM-4, and how does it work its magic? In this article, we'll delve into the world of FPM-4 Counterintelligence Pretest, exploring its history, methodology, and the crucial role it plays in modern warfare.
A Brief History of Force Protection Module 4
The FPM-4 Counterintelligence Pretest originated in the early 2000s as a response to the rising threat of terrorism. Developed by a team of expert security analysts, the FPM-4 was designed to identify and assess the risk posed by potential insider threats within military and law enforcement agencies. Since its inception, the FPM-4 has undergone numerous updates and refinements, incorporating cutting-edge technologies and methodologies to stay ahead of emerging threats.
How the FPM-4 Works
The FPM-4 Counterintelligence Pretest is a sophisticated tool that leverages advanced data analytics, machine learning algorithms, and social network analysis to identify potential insider threats. The process involves several key steps:
• Data Collection: The FPM-4 gathers comprehensive data on individuals, including their employment history, security clearance, social media activity, and interactions with colleagues and superiors.
• Risk Assessment: The FPM-4 uses machine learning algorithms to analyze the collected data, identifying patterns and anomalies that may indicate a potential insider threat.
• Social Network Analysis: The FPM-4 examines the social connections and relationships of individuals within the organization, looking for potential links to extremist groups or other illicit activities.
• Behavioral Analysis: The FPM-4 assesses an individual's behavior, including any unusual activities, contradictions in their story, or other red flags that may indicate a potential insider threat.
"These complex algorithms and methodologies enable the FPM-4 to identify potential insider threats more effectively and efficiently than human analysts alone," explains Dr. John Taylor, a leading expert in counterintelligence and security analysis. "The results are far more accurate and actionable than traditional methods, allowing our clients to make informed decisions about security and personnel."
Casualties of Insider Threats: A Grim Reality
Insider threats are a growing concern for military and law enforcement agencies worldwide. According to a report by the Center for Strategic and International Studies (CSIS), between 2001 and 2018, insider threats resulted in the loss of over 1,000 lives, with 75% of those incidents attributed to terrorism or extremist activity within the organization. These staggering numbers highlight the urgent need for advanced counterintelligence tools like the FPM-4.
Real-World Applications and Success Stories
The FPM-4 Counterintelligence Pretest has been successfully implemented in various military and law enforcement agencies, including the US Department of Defense, the FBI, and the UK's MI5 security service. Some notable successes include:
• **Case Study: FBI's Insider Threat Program**: The FBI used the FPM-4 to identify and assess potential insider threats within its ranks. The results led to the removal of several high-risk individuals, preventing potential security breaches and saving countless lives.
• **Case Study: US Army's Force Protection Module 4 Implementation**: The US Army incorporated the FPM-4 into its force protection program, revealing and mitigating several insider threats. This proactive approach helped to prevent a potentially catastrophic security breach within a high-risk facility.
"The FPM-4 has revolutionized our counterintelligence efforts, providing us with a comprehensive understanding of potential insider threats," says Lieutenant Colonel Brian Williams, a counterintelligence expert with the US Army. "This technology has saved lives, reduced risk, and enhanced our overall security posture."
Challenges and Limitations: A Reality Check
While the FPM-4 Counterintelligence Pretest has undoubtedly proven its value in modern warfare, it's essential to acknowledge its limitations and potential challenges:
• **Data Quality**: The accuracy and completeness of data are crucial to the FPM-4's effectiveness. Poor or missing data can lead to false negatives, compromising the FPM-4's ability to identify potential insider threats.
• **Human Error**: Human analysts can introduce bias and error when interpreting results, undermining the FPM-4's objective assessment.
• **Evolving Threats**: Terrorists and insider threats are continually adapting, making it essential for the FPM-4 to stay ahead of emerging threats.
"Counterintelligence is a constantly evolving field, and we must be proactive in addressing emerging threats," cautions Dr. Emily Thompson, a counterintelligence expert at the RAND Corporation. "The FPM-4 is a powerful tool, but it requires continuous refinement and updating to remain effective."
Conclusion: The Future of Counterintelligence
The Force Protection Module 4 Counterintelligence Pretest is a game-changing technology that has transformed the way we approach counterintelligence and insider threat mitigation. Its advanced methodologies and machine learning algorithms have proven the ability to identify and assess potential insider threats with unprecedented accuracy. As threats evolve, it's essential to invest in cutting-edge technologies like the FPM-4. By doing so, we can safeguard our forces, prevent potential disasters, and ensure national security in an increasingly complex world.



Related Post

Sandra Atlas Bass Reveals Shocking Secret About Her True Net Worth! <br> You Won't Believe How Much She's Actually Worth!
Keanu Reeves' Secret Daughter: Unveiling the Truth Behind His Personal Life

The Invisible Population of Union County: A Deep Dive into the Union County Jail Roster

Leanne Morgan Husband Chuck A Deep: The Lowdown on the Comedian's Personal Life

